Proponents of blockchain which is a distributed ledger technology claim it to be among the best ways to safeguard transactions. How exactly does blockchain security work for government agencies and business networks, beyond transaction and traditional processes?
The blockchain technology has been in effect since around the year 1991. The primary discovery of blockchain was limited to the transaction of currency but in 2014, it witnessed the latest developments and ability in other inter-organizational and financial transaction spaces where the latest opportunities were discovered. And presently, in the last couple of years, the adoption of this technology has increased hugely across the globe in every industry for varied use cases and deployments.
Presently, organizations are taking the advantage of the blockchain technology for handling distributed databases, cybersecurity, digital transaction, and healthcare to create blockchain based solutions for their users. The initial advantage of using this technology is that it makes sure of the security in transactions because of its cryptographic principles, decentralization, and consensus.
A latest report asserts that the global blockchain space is predicted to be valued at $20 billion in 2024. Presently, 69% of banks are exploring varied lanes related to the blockchain technology to make their services consistent, safer, and straightforward.
While blockchain’s adoption has brought many benefits for global organizations, it has also brought in many cybercriminals to get inside the technology and target organizations with cyberattacks. In the present year, blockchain security has become an important part of the working of the organization that is keeping them standing on their knees in the space of hacking and cyberattacks attempts.
In the full guide, we will be having a look at blockchain technology, how its operates, and how to secure it from cyberattacks with the best practices.
What Is Blockchain And How It Operates?
Blockchain is a technology that enables users and entities to store and process information with the structured distributed blocks that are present as a blockchain network. Every latest block stores a transaction or a bundle of transactions that is linked to the previously accessible blocks in the form of a cyptographic chain.
Blockchain operates as a distributed network that enables organizations to connect to it through nodes for the storage and processing of data. The data that is stored in the blocks can be availed with verification, consensus, and validation by the real entity that wishes to store or process the data.
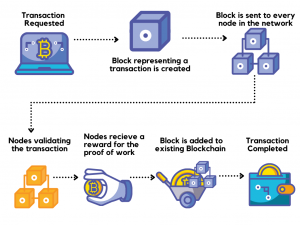
The image above portrays, whenever a transaction is requested by the user by using an application that is based on blockchain, a respective block is formulated in the blockchain network for keeping the data of that transaction. Then the block is again sent to each node in the distributed peer-to-peer network that further validates the transaction. After the process of validation, nodes of the network get a reward for the PoW (Proof of Work). Then the block is added to the prevailing blockchain and the user receives a successful transaction.
Blockchain Security: Recent Cyberattack On Blockchain Solutions
We have witnessed many scenarios in the last few years where blockchain solutions were targeted with cyberattacks and data theft, which enables this technology to be non-immune to cyberattacks even taking into account its default storage security factor. Here are some instances of the latest cyberattack on the blockchain.
- A VC firm named DAO (Decentralized Autonomous Organization) was the victim of a code exploitation attack where it lost Ether that was worth over $60 million.
- Bitcoin that was worth $72 million was robbed from one of the biggest cryptocurrency exchanges named Bitfinex because of stolen keys.
- Another digital currency exchange named Bithumb was recently hacked where the information of closely 30k users were compromised and Bitcoin worth $870k was stolen in a suspected insider job.
Blockchain Security: Definition And Practices
In a gist, blockchain security is a comprehensive risk assessment procedure that is done for the purpose of blockchain solution or network to look after its security. Blockchain security is attained through the implementation of cybersecurity structures, secure coding practices, and security testing methodologies to protect the blockchain network from online breaches, frauds, and other types of cyberattack.
The Best Practices To Build Blockchain Solutions Through Blockchain Security Are:
- To resolve blockchain security issues, enforce and define endorsement agreements that are based on business contracts.
- Allow identity and access management (IAM) controls to handle information access in the blockchain.
- Implement suitable tokens like OAUTH, SAML2, and OIDC to act user authentication, authorization, and verification.
- Safely store identity keys.
- Avail PAM (privileged access management) solution to protect blockchain ledger entries after effective business logic.
- Protect transactions that are based on API with API security best practices.
- Use a data classification strategy to protect user information or data.
- Avail privacy-preserving technologies for the purpose of sensitive information.
- Use standard TLS for external and internal communications.
- Enact multi-factor authentication.
- Keep good cryptographic key management.
- Take advantage of the security incident, hardware security module (HSM), and event management (SIEM).
- Do periodic VAPT (vulnerability assessment and penetration testing)
- Patch security loopholes to safeguard blockchain-based applications from data breaches and vulnerabilities.
The Bottom Line
Blockchain provides various security measures for the solutions that are created on it. However, due to scarcity of exploitable blockchain security vulnerabilities and governance makes it not immune to large scale cyber attacks. Hence, enacting a Blockchain security audit or even penetration testing becomes crucial for your business. The sooner you evaluate the loopholes of blockchain security the sooner you can fix them and safeguard your blockchain solutions from malicious players.
Frequently Asked Questions On Blockchain Security
1. How secure is a blockchain?
Blockchain technology is safe as it is completely distributed and decentralized. There is no single stance of failure, which enables it much harder to corrupt. Hacking into one portion of the system cannot have an impact on other parts. This prevents users from making alterations to the ledger.
2. What is blockchain in cyber security?
Blockchain, which is a DLT (Distributed Ledger Technology), is aimed at formulating trust in an untrusting space, making it a highly strong cybersecurity technology. All nodes can pass along, record, and view any transactional information that is encrypted onto their blockchain.
3. Can blockchains be hacked?
We have witnessed many scenarios in the last few years where blockchain solutions were targeted with cyberattacks and data theft, which enables this technology to be non-immune to cyberattacks even taking into account its default storage security factor.
 Crypto Venture News One stop Crypto Track Down
Crypto Venture News One stop Crypto Track Down