Decentralized Ledger Technology has created new avenues for the entities that are looking for innovation. This is not new and blockchain is among those technologies that have radically altered how industries operate. However, there cannot be one specific solution for the whole sector. So different blockchains are responsible for different roles. In this article, we are going to have a look at the idea of permissioned blockchain.
Every startup, enterprise, company, or a sector is varied when it comes to its requirements and needs. It is true that the companies that are held privately cannot use a completely decentralized blockchain network. That is where varied types of decentralized ledger technology come in.
What Is A Permissioned Blockchain?
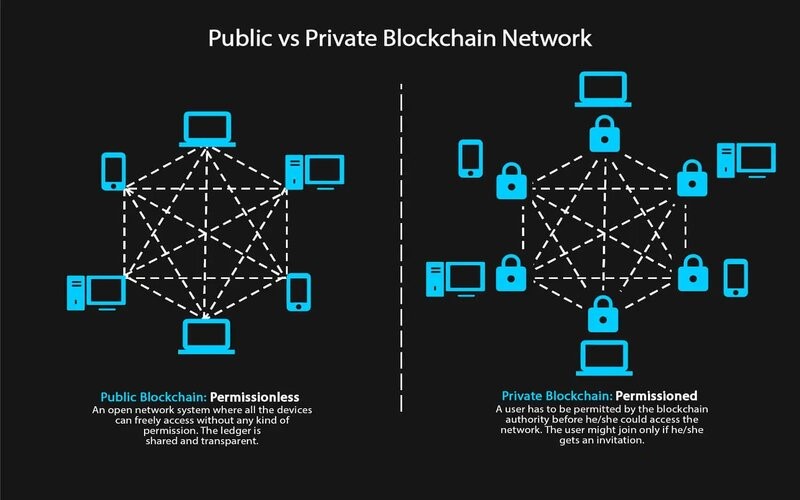
A permissioned blockchain is basically a distributed ledger that is accessible publicly. It is only available to the users with permission. The users in this case can only perform some specified actions granted to them by the administrator of the ledger and are needed to identify themselves via certificates or other virtual means.
You might think of the addition of permissioned users as an added blockchain security mechanism. Administrators in this case maintain an access control layer to enable certain activities to be done only by several identifiable participants. Records are maintained within the blockchain of who is associated with the transactions. This makes permissioned blockchain vary from the public blockchain.
Understanding The Idea Behind Permissioned Blockchain
A blockchain can be constructed and accessed in several ways. Some blockchains require special permissions to access, read, and also write information. Others only need that you have the ability to connect and can carry out the work for the network. The intrinsic configuration of every blockchain controls the transaction of the participants and illustrates their roles where every participant can access and contribute to the blockchain.
It may also involve maintaining the identity of every blockchain participant on the network. Such blockchains are known as permissioned blockchains.
Advantages Of Permissioned Blockchain
There are many advantages of this type of blockchain which makes this technology the most preferable to use when measured opposite to permissionless blockchains. Here are the beneficial characteristics of this blockchain.
Efficient Performance:
When we compare permissioned blockchains to permissionless blockchains, they provide better performance. The primary reason behind this is the limited quantity of nodes on the exchange. This discards the unnecessary computations needed to attain consensus on the network, enhancing the overall performance. Along with that, permissioned networks have their own pre-determined nides for validating a transaction.
Proper Governance Structure:
Permissioned networks do arrive with an appropriate framework of governance. This implies that they are structured. Administrators also need less time to update the regulations over the network, which is relatively faster in comparison to public blockchains. The public network of blockchain suffers from the consensus issue as not all nodes operate together to receive the latest update executed. These nodes might offer their self-interest above the requirements of the blockchain, which, in return, implies slower updates to the complete network. In comparison, a permissioned network does not have the issue, as the nodes function together to move the updates quicker.
Decentralized storage:
Permissioned networks also do proper utilization of blockchain, which involves using its decentralized nature for the storage of data.
Cost-Effective:
There is no confusion that permissioned blockchains are more cost-effective in comparison to the permissionless blockchains.
Disadvantages Of Permissioned Blockchains
This network is not free from drawbacks or disadvantages. With that, let us have a look at the two very prominent disadvantages of permissioned blockchain.
Compromised security
A private blockchain or public blockchain has finer security as the nodes take part in a permissioned blockchain consensus mechanism properly. But, in this case, this might not be true. The security of a permissioned network is as efficient as the integrity of the member. This implies that a small portion of a permissioned mechanism can operate together to alter the data kept within the network. In this method, the integrity of the blockchain can be compromised. To solve it, the system should have effective permissions set so those bad actors cannot integrate together to create the desired effect.
Control, Censorship, and Regulation
In an ideal ecosystem, these permissioned networks should operate as that of a public blockchain, but with rules. However, the regulations join censorship to the network, where the authority can prevent a transaction or handle it from occurring. These are a threat to any organization or business that is using the permissioned network. This procedure also stops the permissioned network from earning the most out of the complete blockchain ecosystem.
Permissioned Vs Permissionless Blockchain: A Small Comparison
There are many differences between permissioned and permissionless blockchains. This comparison is done so that the users can get a clear definition of the implementation of a permissioned network. The following table offers you a quick insight into this comparison.
Permissioned Vs Permissionless Blockchain | ||
Category | Permissioned | Permissionless |
Speed | Faster | Slower |
Privacy | Private membership | Transparent and open - anyone can become a member |
Legitimacy | Legal | Allegal |
Ownership | Managed by a group of nodes pre-defined | Public ownership - no one own the network |
Decentralization | Partially decentralized | Truly decentralized |
Cost | Cost-effective | Not so cost-effective |
Security | Less secure | More secure |
3 Best Permissioned Blockchain Companies
As we can understand, permissioned networks are important to the varied sectors out there. Industries like the supply chain, finance industry, and many more. can be benefited highly via permissioned networks.
The primary permissioned blockchains involve Corda, Quorum, and Hyperledger Fabric. These are the best solutions when it comes to permissioned solutions. Let us look briefly into each of the permissioned blockchains stated below that we think fall in the category of permissioned blockchain examples.
Hyperledger Fabric
Hyperledger Fabric Framework is among the famous Hyperledger ventures that are handled by Linux foundations. The modular framework allows anyone to develop applications or solutions to play and plugin with various services. It utilizes smart contracts called “chaincode” having the logic of the system.
Quorum
Quorum blockchain is a company aimed at Ethereum blockchain that is focused on the financial sector. It was formulated by JP Morgan.
Corda
Corda allows businesses to build interoperable blockchain networks. It is open-source in nature and offers great value to businesses.
Conclusion
It can be concluded that permissioned blockchains are here to stay. They offer blockchain advantages in a closed ecosystem while making sure that it caters to the requirements of an organization. There are obvious advantages of using it, which include cost-effective, efficient performance, and proper governance. However, it also does arrive with its own disadvantages and challenges. So, what is your opinion about permissioned blockchains?
Frequently Asked Questions On Permissioned Blockchain
1. Is Ethereum a Permissioned blockchain?
Initially, Ethereum is a public permissionless blockchain based channel executing a PoW (Proof-of-Work) dependent consensus protocol known as Ethash. Ethereum is also utilized as a private platform.
2. What is Permissioned and Permissionless blockchain?
At the easiest level, the difference depends on whether the design of the blockchain is open for anyone to take part which is permissionless or restricted only to designated participants, or even permissioned.
3. Is Hyperledger a Permissioned blockchain?
Hyperledger Fabric Framework is among the famous Hyperledger ventures that are handled by Linux foundations.
- The Bitcoin Wallet Boom: Why Demand Is Skyrocketing - 25/11/2023
- How To Choose The Best Crypto Exchange Affiliate Programs - 03/03/2023
- Crypto License: How To Get It Now? - 03/02/2023
 Crypto Venture News One stop Crypto Track Down
Crypto Venture News One stop Crypto Track Down